Students must start practicing the questions from CBSE Sample Papers for Class 10 IT with Solutions Set 8 are designed as per the revised syllabus.
CBSE Sample Papers for Class 10 IT Set 8 with Solutions
Time: 2 Hours
Maximum Marks: 50
Instructions
- Please read the instructions carefully.
- This Question Paper consists of 21 questions in two sections: Section A & Section B.
- Section A has Objective Type Questions whereas Section B contains Subjective Type Questions.
- Out of the given (5 + 16 = 21) questions, a candidate has to answer (5 + 10 = 15) questions in the allotted (maximum) time of 2 hours.
- All questions of a particular section must be attempted in the correct order.
- Section A: Objective Type Questions (24 Marks)
- This section has 5 questions.
- Marks allotted are mentioned against each question/part.
- There is no negative marking.
- Do as per the instructions given.
- Section B: Subjective Type Questions (26 Marks)
- This section has 16 questions.
- A candidate has to do 10 questions.
- Do as per the instructions given.
- Marks allotted are mentioned against each question/part.
Section A
Objective Type Questions
Question 1.
Answer any 4 out of the given 6 questions based on Employability skills. (4 × 1 = 4)
(i) Smriti is a brilliant student. She studies well, has joined many extra-curricular activity groups, learned swimming etc. You can say that she has too much on her plate. What type of stress she might suffer from? (1)
(a) Survival stress
(b) Internal stress
(c) Fatigue related stress
(d) Environmental stress
Answer:
(c) Fatigue related stress
(ii) Anamika never resents others because she is pretty clear about her ambitions, emotions, abilities, interests etc. She also makes conscious efforts to learn more about her own beliefs, likes and dislikes. This is called _______ (1)
(a) stress
(b) self-awareness
(c) self-motivation
(d) self-regulation
Answer:
(b) self-awareness
(iii) Sunaina wants to replace some data in her Word document. Which shortcut keys could she use? (1)
(a) Ctrl + F
(b) Ctrl + V
(c) Ctrl + Z
(d) Ctrl + H
Answer:
(d) Ctrl + H
(iv) Energy demand in developing countries will increase to _______ times the current levels by 2030. (1)
(a) four
(b) five
(c) six
(d) eight
Answer:
(c) six
(v) Ram wants to have his own business and become an entrepreneur. His father warned him about one disadvantage of this career. What it might be? (1)
(a) Independence
(b) Ambition fulfillment
(c) Uncertainty
(d) None of the above
Answer:
(c) Uncertainty
![]()
(vi) Flow would you describe feedback that helps the learner understand what they need to improve? (1)
(a) Descriptive
(b) Specific
(c) General
(d) Sign
Answer:
(a) Descriptive
Question 2.
Answer any 5 out of the given 6 questions. (5 × 1 = 5)
(i) A _______ is a model that you use to create other documents. (1)
(a) template
(b) document
(c) design
(d) copy paste
Answer:
(a) template
(ii) In a document, _______ is used to apply a style to many different areas quickly without having to go back to the Styles and Formatting window and double-click every time. (1)
(a) Fill format mode
(b) Formatting window
(c) Painter mode
(d) Text wrapping
Answer:
(a) Fill format mode
(iii) In a document, _______ refers to the vertical or horizontal placement of a graphic about the chosen anchor point. (1)
(a) arrangement
(b) anchoring
(c) alignment
(d) text wrapping
Answer:
(c) alignment
(iv) Tanu explained to his class that to apply an existing style, except for _______ position the insertion point in the paragraph, frame or page and then double-click on the name of the style in one of these lists. (1)
(a) Window style
(b) Character style
(c) Paragraph style
(d) Cell style
Answer:
(a) Window style
(v) Symbol option is available under _______ group in the Insert tab. (1)
(a) Symbols
(b) Font
(c) Header
(d) Footer
Answer:
(a) Symbols
(vi) After selecting the text you need to click the _______ in the font group to make the font size larger than the current font size. (1)
(a) Text size
(b) Font size
(c) Font type
(d) Capital letters
Answer:
(b) Font size
Question 3.
Answer any 5 out of the given 6 questions. (5 × 1 = 5)
(i) Arguments passed to a macro from Calc are always _______ (1)
(a) strings
(b) references
(c) numbers
(d) values
Answer:
(d) values
(ii) _______ function takes data from a series of worksheets or workbooks and summarizes it into a single worksheet that you can update easily. (1)
(a) Summation
(b) Data Consolidation
(c) Data Format
(d) Data Chart
Answer:
(b) Data Consolidation
(iii) AutoSum option is available in (1)
(a) Home tab
(b) View tab
(c) Insert tab
(d) Layout tab
Answer:
(a) Home tab
(iv) Which of the following components provides additional information in the chart? (1)
(a) Legend
(b) Gridlines
(c) Data label
(d) Plot area
Answer:
(c) Data label
![]()
(v) Which function cannot be performed through Subtotal in a Spreadsheet? (1)
(a) Sum
(b) Product
(c) Average
(d) Percentage
Answer:
(d) Percentage
(vi) To enter the current time in Calc, you need to press _______ (1)
(a) Ctrl + Alt +;
(b) Shift + Alt +;
(c) Ctrl + Shift +;
(d) None of these
Answer:
(c) Ctrl + Shift +;
Question 4.
Answer any 5 out of the given 6 questions. (5 × 1 = 5)
(i) The _______ has evolved since the 1960s to ease increasing difficulties in designing, building, and maintaining complex information systems. (1)
(a) Knowledge concept
(b) Formula concept
(c) Database concept
(d) Forms concept
Answer:
(c) Database concept
(ii) Out of the following, which one is the most appropriate data field in the context of the employee table, if only one of these is required? (1)
(a) Age in years
(b) Date of birth
(c) Age in days
(d) Age in months
Answer:
(b) Date of birth
(iii) Malini wants to store a huge amount of information about her zone in a database. Her friend Gargi explained to her about various benefits of storing data in RDBMS. It helps in preventing/controlling duplication of data. Which of the following terms is used to refer to duplication data? (1)
(a) Data sharing
(b) Data Privacy
(c) Data redundancy
(d) Data integrity
Answer:
(c) Data redundancy
(iv) For what, Memo data type is used? (1)
(a) To add table
(b) To store objects created in other programs
(c) For long text entries
(d) For short text entries
Answer:
(c) For long text entries
(v) Attribute is a unique identifier for each tuple. It is defined in the form of (1)
(a) rows
(b) columns
(c) tree
(d) query
Answer:
(b) columns
(vi) Which of the following commands is used to retrieve data from a database? (1)
(a) SELECT
(b) COPY
(c) OPEN
(d) RETRIEVE
Answer:
(a) SELECT
Question 5.
Answer any 5 out of the given 6 questions. (5 × 1 = 5)
(i) Which of the following is the first network? (1)
(a) ARPANET
(b) Internet
(c) NSFnet
(d) NET
Answer:
(a) ARPANET
(ii) Which of these services will not be provided by a typical Internet Service Provider (ISP)? (1)
(a) An E-mail address
(b) Modem
(c) A connection to the Internet
(d) Technical help
Answer:
(a) An E-mail address
(iii) _______ is an example of a text-based browser which provides access to the Internet in the text-only mode. (1)
(a) Mozilla Firefox
(b) Lynx
(c) Internet Explorer
(d) All of these
Answer:
(b) Lynx
(iv) Nick connects to the Internet at home using a laptop computer with a wireless connection.
Nick is going to change to a desktop computer using a 1 Gbps ethernet cable connection.
Which of these should be the result of making the changes? (1)
(a) Increased portability and decreased speed
(b) Decreased portability and increased speed
(c) Increased portability and increased speed
(d) Decreased portability and decreased speed
Answer:
(b) Decreased portability and increased speed
(v) Which of the following websites is used for booking train tickets? (1)
(a) Nykaa
(b) IRCTC
(c) RedBus
(d) Myntra
Answer:
(b) IRCTC
(vi) Qumana is an offline blog editor that is used for _______ operating system(s). (1)
(a) Windows
(b) Mac
(c) Both (a) and (b)
(d) None of the above
Answer:
(c) Both (a) and (b)
Section B
Subjective Type Questions
Answer any 3 out of the given 5 questions on Employability skills. Answer each question in 20-30 words. (3 × 2 = 6)
Question 6.
How can one adapt their communication style to different audiences? (2)
Answer:
Adapting communication style involves understanding the audience’s needs, preferences, and cultural background. It requires using appropriate language, tone, and examples to ensure the message is understood and well-received.
![]()
Question 7.
It is important to be in charge of your own self and not be charge of your own self and not be dependent on anyone else in life. List any two reasons for which self-regulation is a must. (2)
Answer:
Self-regulation is important in life for to following reasons:
- Self-regulation allows you to keep a tab on your own emotions.
- Self-regulation enables to development of the idea of ‘what is appropriate behaviour’ and ‘what is inappropriate behaviour’ in a given social condition.
Question 8.
What general precautions should you take while cleaning the computer/components? (2)
Answer:
- Always Power off the computer system before cleaning.
- Never spray cleaning fluid directly on the components of the computer. First, spray the liquid on the cloth and then wipe the component.
- Do not allow the cleaning liquid to drip near the circuit board.
- Preferably use an anti-static wrist band which helps to prevent the building up of static electricity near electronic devices.
Question 9.
Can green skills help in achieving the Sustainable Development Goals (SDGs)? (2)
Answer:
Yes, green skills are essential for achieving the SDGs, as they contribute to goals related to clean energy, sustainable cities, responsible consumption and production,’climate action, and life below water and on land.
Question 10.
Write about any two myths and their truth regarding entrepreneurship. (2)
Answer:
The common set of myths of entrepreneurship is explained below:
- Talent is More Important than Industry: This is not true as the nature of the industry an entrepreneur chooses greatly affects the success and growth of the business.
- Most Start-ups are Successful: Mostly in developing countries start-ups fail as they cannot manage to earn high profits.
Answer any 4 out of the given 6 questions in 20-30 words each. (4 × 2 = 8)
Question 11.
Differentiate between the Save and Save As options. (2)
Answer:
‘Save’ means the file gets saved under its current name, in whatever folder it was saved before or in the default folder of that computer, whereas ‘Save As’ gives you the opportunity to save the file under a different name and in another folder. ‘Save As’ allows you to name the updated version with a new name and at the same time preserve the old version.
Question 12.
What, makes a workbook different from a worksheet? (2)
Answer:
Differences between the workbook and worksheet are as follows:
| Workbook | Worksheet |
| A workbook is an Excel file with one or more worksheets. | A worksheet is a single spreadsheet of data. |
| A workbook would be the entire binder, with everything in it. | A worksheet would be like one section in that binder. |
Question 13.
What is the use of cell reference? (2)
Answer:
To avoid writing the data again and again for calculating purposes, cell reference is used. When you write any formula, for a specific function, you need to direct Excel to the specific locator of that data. This location is referred to as, cell reference. So, every time a new value is added to the cell, the cell will calculate according to the reference cell formula.
Question 14.
Describe the significance of the primary key in a database. (2)
Answer:
The primary key is used to uniquely identify the record in a database. It can be a column or a set of columns in the table. The main features of the primary key are as follows:
- It must contain a unique value for each record of the table.
- It does not contain null values.
Question 15.
Elucidate the following terms: (2)
- PAN
- WIMAX
Answer:
- PAN: It stands for Personal Area Network. It is a computer network used for communication among computers and different technological devices close to it.
- WiMAX: It stands for Worldwide Interoperability for Microwave Access. It is a wireless transmission of data using a variety of transmission modes.
Question 16.
Why is it important to secure the internet? What are the uses of it? (2)
Answer:
Your passwords are the most common way to prove your identity when using websites, e-mail accounts, and your computer itself. The use of a strong password is therefore essential in order to protect your security and identity.
Answer any 3 out of the given 5 questions in 50-80 words each. (3 × 4 = 12)
Question 17.
How to resize an image? (4)
Answer:
Resizing a drawing object is done the same as image resizing. To resize a drawing object, follow the below steps:
- Click the object to show the green resizing handles.
- Position the pointer over one of the green resizing handles. The pointer changes shape giving a graphical representation of the direction of the resizing.
- Click and drag to resize the object.
- Release the mouse button when satisfied with the new size.
![]()
Question 18.
Elucidate the following with examples. (4)
(i) Goal seek
(ii) Scenario
Answer:
(i) Goal seek: It refers to the act of determining your input value based on a previously determined output value. The method entails the use of a certain operator in a formula that may be calculated with computer software, eg. Set Cell This specifies the cell whose value will be changed to the desired value after the Goal seek operation is completed.
(ii) Scenario: Scenarios are a tool to text “What-if” questions. Each scenario is given a unique name which can be changed and presented independently. Only the content of the currently active scenario is printed when printing the spreadsheet. It is a set of saved values that we may use in four calculations and using the Navigator or a drop-down list displayed beside the changing cells, we may simply switch between these sets.
Question 19.
Write SQL queries for the questions from (a) to (d) based on table Class. (4)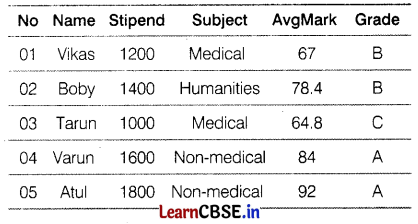
(a) Select all the non-medical stream students from the class table.
(b) List the names that have grade A sorted by stipend.
(c) Arrange the records of class name-wise.
(d) List the records whose grade is B or C.
Answer:
(a) SELECT * FROM Class WHERE Subject=‘Non-medical1;
(b) SELECT Name FROM Class WHERE Grade=‘A’ ORDER BY Stipend;
(c) SELECT * FROM Class ORDER BY Name:
(d) SELECT * FROM CLASS WHERE GRADE = ‘B’ OR GRADE = ‘C’:
Question 20.
Discuss the components of a database. (4)
Answer:
A database consists of several components. Each component plays an important role in the database system environment. The major components of the database are as follows:
- Data: It is raw numbers, characters, or facts represented by value. Most organizations generate, store, and process large amounts of data. The data acts as a bridge between the hardware and the software. Data may be of different types such as User Data, Metadata, and Application Metadata.
- Software: It is a set of programs that lies between the stored data and the users of the database. It is used to control and manage the overall computerised database. It uses different types of software such as MySQL, Oracle, etc.
- Hardware: It is the physical aspect of the computer, telecommunication, and database, which consists of the secondary storage devices such as magnetic disks, optical discs, etc., on which data is stored.
- Users: Several users can access or retrieve the data on demand using the application and the interfaces provided by DBMS.
Question 21.
What is network topology? Also, discuss the different types of topologies. (4)
Answer:
The network topology refers to the arrangement or pattern of computers, which are interconnected in a network. Commonly used network topologies are as follows:
Bus Topology:
It is a type of network in which the computers and the peripheral devices are connected to a common single-length data line All the computers or devices are directly connected to the data line. The data is transmitted in small blocks known as packets.
Ring or Circular Topology:
In this type of topology, each node is connected to two neighboring nodes. the data transferred direction only from one node to another node around the ring. After passing through each node the data returns to the sensing node.
![]()
Star Topology:
In this topology, there persists a central node called a server or hub, which is connected to the nodes directly. If a node has to take information from another ncce then the data is taken from that node through the central node or server.
Mesh Topology:
In this topology, each node is connected to more than one node, so that it provides an alternative route, in case, the host is either down or busy. It is also called a completely interconnected network. We can also call it an extension to the P2P network.
Tree Topology:
It is an extension and variation of bus topology. Its basic structure is like an inverted tree, where the root acts as a server. In tree topology, the node is interlinked in the form of a tree. If one node fails, then the node following that node gets detached from the main tree topology.